In a digitally interconnected world, healthcare professionals face an ever-growing challenge: protecting vital medical data from mounting cyber threats. The healthcare sector is under constant pressure to deliver quick and accurate diagnoses, yet malicious actors find new ways to exploit system vulnerabilities, putting patient data at risk.
When a Picture Archiving and Communication System (known as the picture archiving) goes unprotected, the consequences can be devastating—ransomware attacks, unauthorized access, and even the shutdown of critical system functions. These cybersecurity incidents lead to enormous operational and financial strain, shaking patient confidence and threatening lives.
The good news is that by leveraging proven strategies and commercially available cybersecurity technologies, healthcare institutions can significantly strengthen the security of the PACS environment. In this blog post, we’ll delve into the topic of cybersecurity for PACS, explore the best practices found in the literature on cybersecurity in healthcare, and highlight solutions like Radsource’s ProtonPACS so you can reduce cybersecurity risk. Read on to discover a structured roadmap toward implementing cybersecurity in healthcare information technology.
Key Takeaways
- Key Takeaway #1: PACS-specific security measures must be prioritized, as imaging plays an important role in diagnoses and treatment.
- Key Takeaway #2: Implementing cybersecurity frameworks and best practices—like the NIST Cybersecurity Framework—protects patient data and ensures the performance and usability of PACS.
- Key Takeaway #3: Solutions like ProtonPACS offer robust safeguards, from strong encryption to role-based access, helping healthcare institutions stay ahead of cybersecurity threats.
What is PACS?
PACS would refer to a management system for storing, retrieving, and distributing medical imaging 1995 documents and files. In full, PACS stands for Picture Archiving and Communication System, and it plays a strong point of the PACS infrastructure by enabling healthcare professionals to conveniently access and share diagnostic images. Known as the picture archiving and communication system, it is a cornerstone in modern imaging informatics.
Why is Cybersecurity Essential?
Cybersecurity challenges have rapidly evolved, impacting the healthcare sector at an alarming rate. With the increasing adoption of medical devices and the reliance on imaging files to guide patient care, the risk of unauthorized access has surged. Publications discussing specific cybersecurity topics show that failing to secure PACS and medical imaging devices can lead to compromised patient data. Moreover, the Department of Homeland Security and other agencies highlight how critical it is to protect PACS from breaches that disrupt operations.
Ensuring a secure PACS is vital for safeguarding Americans’ medical images and data, maintaining operational efficiency, and upholding the trust that patients place in healthcare providers. In fact, the “national infrastructure protection plan provides a healthcare lens through its infrastructure protection plan – healthcare chapter, urging more robust measures. Let’s now explore how to strengthen PACS to defend against modern cybersecurity threats.
The Importance of Cybersecurity in Picture Archiving Systems
PACS in Radiology
In radiology, communication systems like PACS and medical imaging are essential for timely diagnoses and treatment planning. PACS environment technology integrates seamlessly with other systems, including imaging modalities support such as X-ray, computed tomography, and magnetic resonance imaging.
Risks of Unsecured PACS
When a PACS network is exposed to cybersecurity threats, the security of the PACS becomes jeopardized. Breaches can lead to severe repercussions, from patient privacy violations and hefty fines to complete operational paralysis. Healthcare information can be manipulated or stolen, resulting in compromised diagnoses and eroded patient trust.
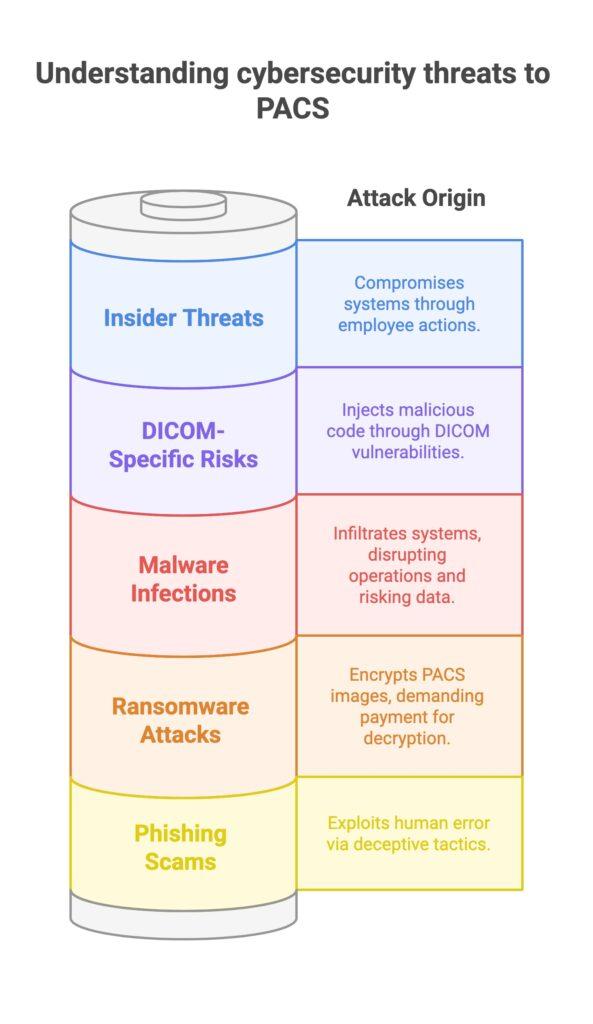
Common Cybersecurity Threats to PACS
Ransomware Attacks
Ransomware is one of the most prevalent cybersecurity threats, targeting PACS and medical imaging to extort money from healthcare institutions. Attackers encrypt critical images in the PACS, rendering them inaccessible until a ransom is paid. Such attacks are especially damaging in a PACS environment by using weaknesses in older systems to gain entry and disrupt patient care.
Phishing Scams
Phishing is a specific cybersecurity threat that exploits human error. Unsuspecting staff members can click on malicious links or enter credentials on fake login pages, granting attackers backdoor entry to sensitive data. Healthcare and public health sector-specific phishing campaigns are increasingly common, making staff awareness crucial to prevent broader compromises within the archiving and communication system.
Malware Infections
Malware is designed to infiltrate a computer system and disrupt normal operations. In a PACS ecosystem, malware might spread rapidly across integrated communication systems, putting both medical data and the performance and usability of PACS at risk. Healthcare institution leaders must deploy robust anti-malware solutions to protect the integrity of imaging data.
Insider Threats
An often overlooked aspect of general cybersecurity is insider threats. Sometimes unintentional, sometimes malicious, employees can compromise systems by sharing login credentials or mishandling patient data. Even a single workstation to notify the PACS of new studies can become a gateway for breaches if security protocols are not strictly followed.
DICOM-Specific Risks
DICOM (Digital Imaging and Communications in Medicine) is widely adopted for exchanging images. However, vulnerabilities in imaging and communications in medicine can allow malicious code injections. This scenario underscores why cybersecurity in healthcare and a robust plan – healthcare and public sector coverage is essential to defend against advanced threats lurking within DICOM transmissions.
Vulnerabilities in PACS Systems
Network Exposure
Direct Internet connectivity of a PACS server about the user can open gateways for cybercriminals. Without adequate firewalls or segmentation, attackers can exploit a PACS network. The vulnerability increases if the infrastructure is not maintained under current cybersecurity standards and best practices outlined by the NIST Cybersecurity Practice Guide.
Access Control Issues
Weak passwords, absence of multi-factor authentication, and poor role management can lead to unauthorized access. When PACS specific security measures must be enforced yet are overlooked, the system becomes an easy target for hackers. This risk is amplified in larger organizations, where numerous users access the system daily.
Outdated Software
One of the biggest cybersecurity measures is ensuring regular updates. Older software can have unpatched vulnerabilities that attackers easily exploit, putting the security of the system at risk. Implementing cybersecurity best practices also includes routine assurance testing of the imaging device and immediate patch deployments to prevent known exploits.
Cloud Storage Challenges
As healthcare organizations shift toward cloud-based solutions, misconfigurations or lack of encryption can open the door to data breaches. Infrastructure protection plan – healthcare guidelines recommend encrypting imaging files at rest and in transit. When applying the “specific cybersecurity topics that apply to PACS,” ensuring robust authentication and encryption is key for safe cloud adoption.
Advanced Security Measures for Secure PACS Systems
Encryption
Encrypting both data at rest and in transit is crucial for preventing unauthorized access. In fact, integrating the healthcare enterprise often relies on a combination of standard encryption protocols, ensuring that imaging data and other sensitive details remain protected end-to-end. This approach helps protect patient data from eavesdropping or tampering.
Role-Based Access Controls
Only authorized personnel should be able to view or modify medical image data. Role-based access ensures each individual in a healthcare institution can only perform tasks appropriate to their duties. This approach sharply reduces the chance of inadvertent data leaks or malicious exploitation, safeguarding your picture archiving and communication strategy.
Network Segmentation
Separating a PACS environment from other systems, like general business applications, drastically limits a cyber attacker’s ability to move laterally. This approach, endorsed by the Department of Homeland Security, effectively narrows the threat surface within your archiving and communication architecture.
Intrusion Detection Systems (IDS)
An intrusion detection system actively monitors traffic and alerts administrators to suspicious activity. This measure is one of the most effective ways for healthcare institutions to detect infiltration early, allowing timely intervention before data is compromised. It’s part of the broader plan – healthcare and public frameworks for advanced threat monitoring.
DICOM Image De-Identification
Removing personal details from medical image data is a critical layer in reducing cybersecurity risk. By stripping away identifiers, any breach that might occur has fewer repercussions for patient privacy. This technique matches well with topics that apply to PACS in the NIST cybersecurity practice guide, ensuring compliance while preserving diagnostic quality.
Implementing a Robust Cybersecurity Strategy
Regular Software Updates
Performing timely system updates is essential in staying ahead of newly discovered vulnerabilities. Hdos implements current cybersecurity standards by routinely patching operating systems, applications, and the PACS server. Testing of the imaging device after updates ensures minimal downtime and safeguards against known exploits in the PACS environment.
Staff Training and Awareness
The human factor remains a significant vulnerability. A single click on a malicious email can compromise the entire computer system. Ongoing training sessions, simulated phishing exercises, and clear guidelines on safe web practices are all part of implementing cybersecurity best practices to reduce cybersecurity risk.
Incident Response Planning
Even the most advanced systems cannot eliminate all cybersecurity incidents. Therefore, having a plan for quick mitigation is imperative. An effective incident response plan includes immediate isolation of the affected network segment, thorough investigation, and transparent communication with stakeholders, ensuring minimal disruption to patient care.
Collaboration with Specialists
Whether through direct partnerships with PACS vendors or national cybersecurity experts, collaborating with specialists is critical. Many organizations turn to professional services that conduct assurance testing of the imaging and PACS system. Such collaborations accelerate the adoption of new security measures and best practices, aligning them with healthcare information technology in general.
How Radsource’s ProtonPACS Stands Out
Overview of ProtonPACS
Radsource’s ProtonPACS is a prime example of a secure PACS solution designed with specific cybersecurity priorities in mind. This robust platform publishes studies related to cybersecurity while maintaining the flexibility and speed needed for modern clinical workflows. Built from the ground up, it accommodates advanced imaging informatics and ensures the performance and usability of PACS is not compromised.
Security Features of ProtonPACS
ProtonPACS is built on the premise that the security of the system must come first. Here are some highlights:
- Built-in encryption for secure data handling. Data is encrypted at every stage, reducing the likelihood of breaches.
- Role-based access control and multi-factor authentication. Ensures that only those with the right clearance can access critical imaging data.
- Regular updates to address new cybersecurity threats. Frequent patches keep attackers from exploiting newly discovered vulnerabilities.
- Customizable protocols for compliance with healthcare regulations. This aligns with integrating the healthcare enterprise guidelines, ensuring your PACS ecosystem by using ProtonPACS meets compliance benchmarks.
Why Choose ProtonPACS?
Radsource’s ProtonPACS represents the strong point of the PACS community’s collective knowledge and experience. Its architecture helps healthcare organizations protect Americans’ medical images and data more effectively, thereby reinforcing trust. By leveraging the cybersecurity framework and other relevant standards, ProtonPACS remains an invaluable tool for any healthcare institution aiming to safeguard patient data and maintain operational reliability.
Conclusion
Cybersecurity in healthcare is non-negotiable. PACS would be incomplete without robust defenses, as they handle crucial imaging data pivotal to patient well-being. Prioritizing a topic of cybersecurity for PACS ensures greater resilience and peace of mind.
Radsource’s ProtonPACS stands out for its advanced security protocols, leveraging NIST cybersecurity practice guide principles and other specific cybersecurity topics that apply to pacs. By embracing solutions like ProtonPACS, healthcare organizations can stay ahead of emerging threats.
Ready to fortify your picture archiving and communication (archiving and communication) approach? Reach out to Radsource and explore ProtonPACS. Take the first step in building a more secure, future-proof medical image infrastructure for your healthcare institution.